What do the library at the University of Ottawa and Dan Levy, who played David on Schitt’s Creek, have in common? The Indigenous Canada MOOC! Librarians at the University of Ottawa also provided opportunities for colleagues to complete the MOOC in 2019 – 2020.

Information warfare
While information as a strategic resource is not a new concept, information warfare (IW) is a relatively recent term and may be one that library staff members have yet to encounter. IW involves the manipulation of information to achieve specific goals. It includes spreading disinformation for purposes such as terrorism and political gain but can also include attacks on information systems and networks, deliberate assaults on the free flow of reliable and authentic information, the manipulation of computer networks to cause chaos, the invasion of privacy for espionage or theft, and so on. IW is increasingly common, and both states and non-state entities may find that they are targets.
In this High 5 column, author Jennifer Dekker will provide an overview of five different types of IW, recognizing that threats are always evolving.
1. Political uses
IW is used for specific political goals. For example, in June 2019, the president of the United States opted not to engage in physical warfare on the state of Iran and instead carried out a cyberattack on computer systems that control Iran’s rocket and missile launchers. In this case, IW was employed to achieve foreign-policy goals and to provide a strong warning to a foreign state without causing physical damage or death to a civilian population, unlike in traditional warfare.
Another familiar example of using IW to achieve political goals is WikiLeaks, which publishes leaked confidential documents on its online platform. WikiLeaks’ objective is to expose corruption, thereby impacting governance. However, this exposure has damaged traditional relationships between states, and WikiLeaks is often viewed as a threat to state security. It has been accused of interfering in free and democratic elections, particularly in the U.S., where it leaked private emails and information about one presidential candidate in the 2016 election.
2. Terrorism
Social media platforms are the dominant delivery system for terrorism-related IW. The platforms are used to convince readers of the goodness, power and justice of various terrorist networks. The Islamic State is well-known for its sophisticated and effective social media marketing and its corresponding success in recruiting new members, but many other terrorist groups use social media for the delivery of IW, a strategy which increases their ability to carry out physical attacks.
3. Computer security
Attacks on institutions to steal personal, financial or other data occur regularly. Phishing emails, messages containing computer viruses and malware, as well as hacking into accounts, put everyone who uses computers at risk of identity theft and financial loss. Password managers can be employed to increase the security of accounts, and many institutions are now delivering cybersecurity training to protect their systems, and the personal accounts of their clients, from IW.
Massive cyberattacks, with the potential to destabilize entire states and populations, are also increasing in frequency. These attacks often combine several different goals and tactics. For example, Russian hackers shut down the power grid in the Ukraine twice in recent years for politically motivated reasons, causing chaos and uncertainty.
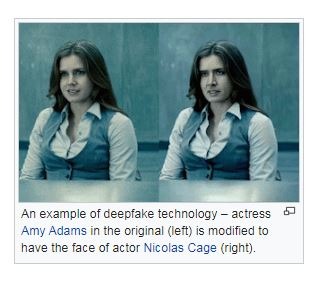
4. Photorealist audio and video (deepfakes)
Deepfakes are images or audio files that have been manipulated to deceive. Faces may be altered to show individuals doing and saying things that are usually very damaging. Deepfakes increase the possibility of propaganda and personal harassment. They are very often used in personal attacks such as revenge pornography. Artificial intelligence is being used to develop increasingly sophisticated tools for creating deepfakes, making these images and audio files very difficult to identify.
5. Personal data and targeted online advertising
By now, most of us know that the Brexit/Leave campaign in the United Kingdom achieved its goal through contracts with Facebook and the now-defunct Cambridge Analytica. These companies gathered millions of data points about users and targeted them with advertising intended to persuade users to vote to leave the European Union. Certain details were recently revealed in a Netflix documentary called The great hack, which also describes how the 2008 and 2016 U.S. elections were similarly influenced. Because social media platforms are so widely used and people share so much personal information, companies exploit personal data and send targeted advertising intended to influence how people vote.
Although these are just five different manifestations and goals of IW, information workers must be aware of the ways in which information is being used to accomplish very specific and often nefarious goals. Know how information is used to accomplish specific, often nefarious goals. Whereas traditional physical warfare has long-standing and international agreed-upon laws, IW has no physical boundaries and is subject to very few laws; therefore, we librarians and information workers should increase our own awareness of and defences against threats.
With greater knowledge, we can help our library users and one another to identify hazards and to prevent some attacks. It is also a critical time to ensure that we are promoting legitimate, high-quality information and good cybersecurity habits.
Wordcloud by Martha Attridge Bufton
Jennifer Dekker is a Subject Specialist Librarian at the University of Ottawa serving the Faculty of Arts. She can be reached at jdekker [at] uottawa.ca.
